Seldom has a single cybersecurity breach posed such a far-reaching threat to the global software ecosystem. On March 31, 2026, security firm StepSecurity identified two malicious versions of the Axios library published to the npm registry. Axios, an HTTP client with approximately 83 million weekly downloads, serves as a foundational component across countless applications. The compromised versions, 1.14.1 and 0.30.4, were engineered to covertly install a Remote Access Trojan on affected systems.
The perpetrators executed the attack by hijacking the npm account of the primary Axios maintainer. Having gained unauthorized access, they changed the account's registered email to an anonymous address. They then bypassed the project's standard security pipeline and published the poisoned packages directly. Both release branches were compromised within 39 minutes of each other, maximizing potential exposure.
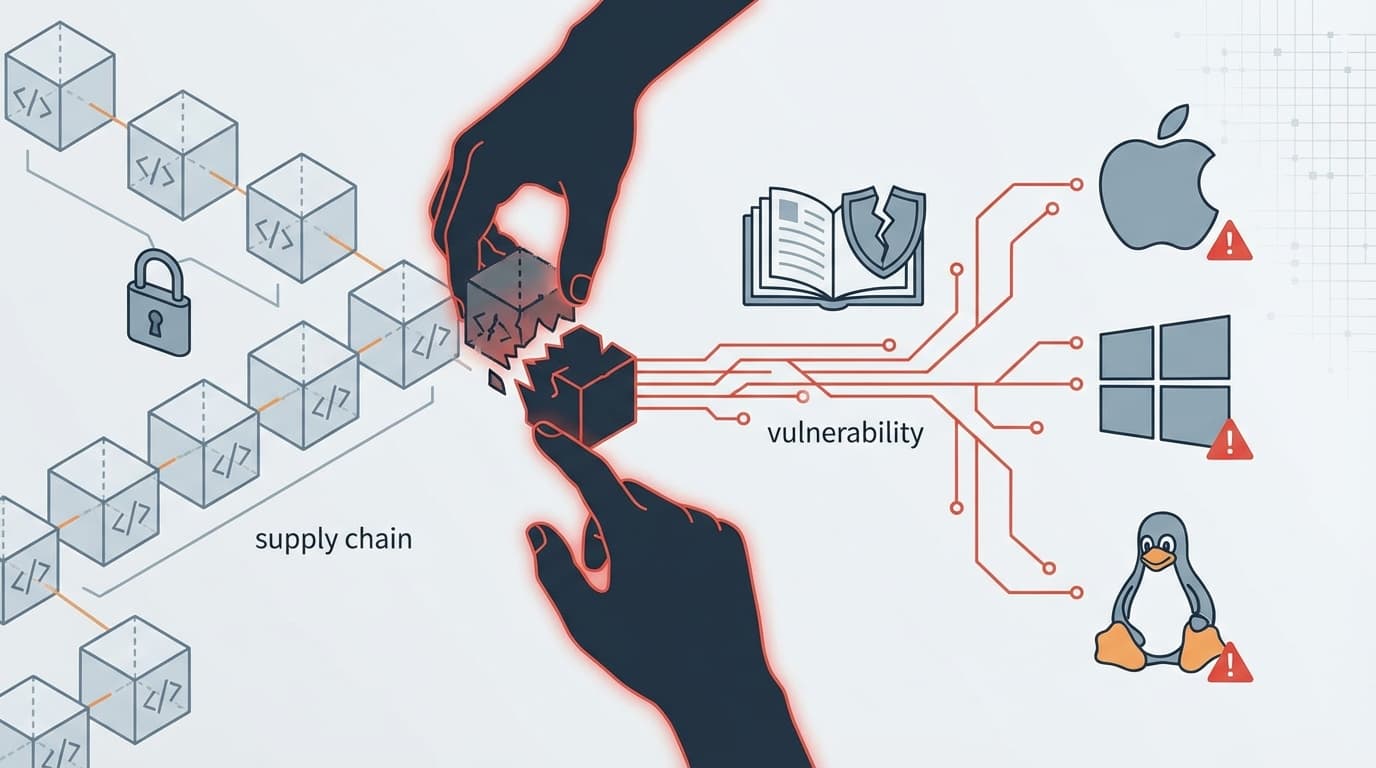
What renders this attack particularly insidious is its operational sophistication. The malicious dependency was staged 18 hours before the compromised Axios versions appeared. After installation, the malware contacted a command-and-control server and delivered platform-specific payloads for macOS, Windows, and Linux. The dropper subsequently erased itself and replaced its own files with clean decoys, leaving virtually no forensic trace.
The coordinated response from the cybersecurity community proved instrumental in mitigating the damage. Automated detection systems flagged the anomalous package within minutes of its publication. GitHub swiftly suspended the compromised account, and npm removed the malicious versions. Nonetheless, the poisoned packages remained available for nearly three hours, a window sufficient to affect numerous developers worldwide.
This incident underscores a fundamental vulnerability inherent in open-source software supply chains. When a single compromised credential can distribute malware to millions of users, the prevailing security model warrants rigorous reassessment. Security experts now recommend that organizations audit their dependencies, rotate all credentials, and implement stricter publishing safeguards. Had such preventive measures been universally adopted, the impact might have been substantially diminished.